AADInternals World Tour August 2022: USA
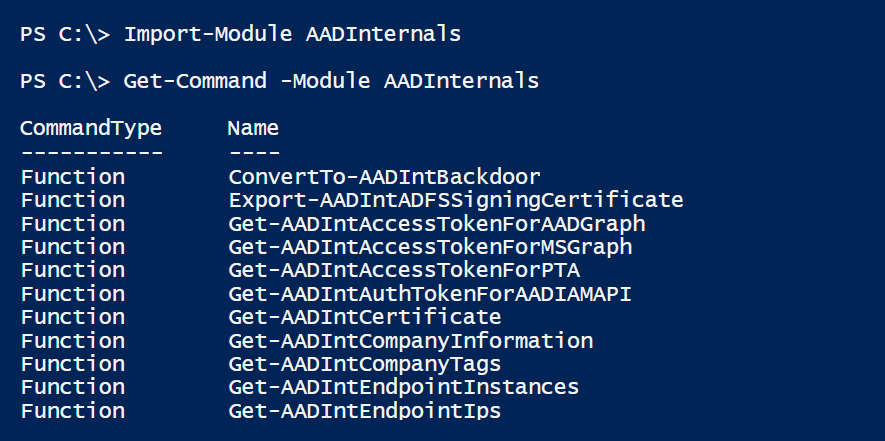
In August 2022, I’ll have several presentations regarding Azure AD security, open-source tools, and bug bounties.
I’ll be presenting at TECHMENTOR, Black Hat Arsenal, DEF CON demo labs, and Cloud Village.
If you like to have a chat on anything Azure AD related, want to say hi or get AADInternals sticker, check my schedule!