Journey to Azure AD PRT: Getting access with pass-the-token and pass-the-cert
Lately we have seen great articles by @_dirkjan, @tifkin_, @rubin_mor, and @gentilkiwi about utilising Primary Refresh Token (PRT) to get access to Azure AD and Azure AD joined computers.
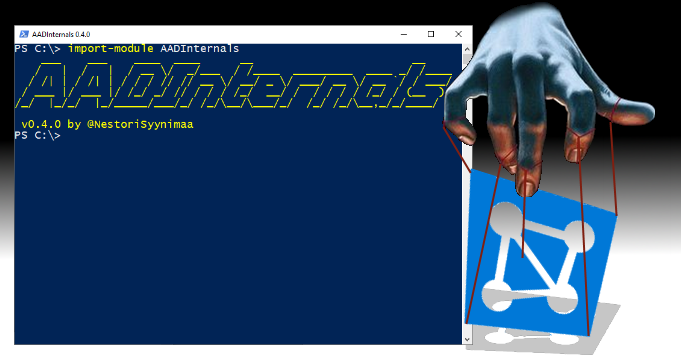
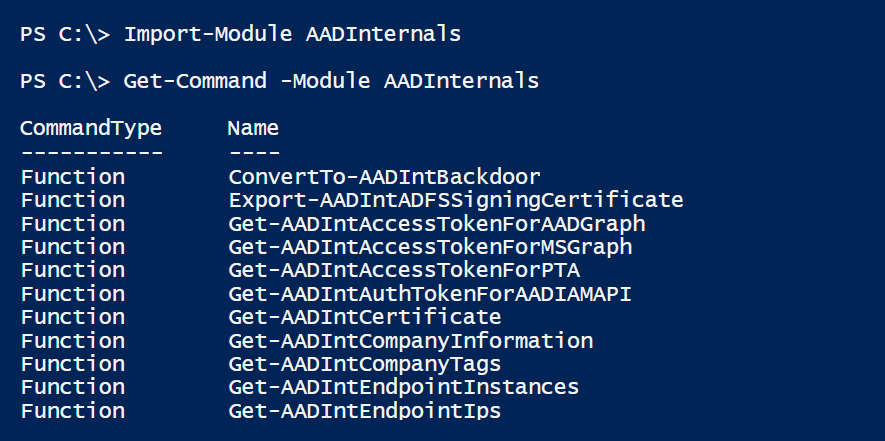
In this blog, I’ll report my own findings regarding to PRT and introduce the new functionality added to AADInternals v0.4.1.