Deep-dive to Azure AD Pass-Through Authentication
In my earlier blog, I explained how Azure AD identity federation works under-the-hood. In this post, I’ll be doing the same with Azure AD pass-through authentication (PTA).
In my earlier blog, I explained how Azure AD identity federation works under-the-hood. In this post, I’ll be doing the same with Azure AD pass-through authentication (PTA).
In my earlier blog post I explained how to create a backdoor to Azure AD using an identity federation vulnerability feature I discovered in 2017.
In this blog post, I’ll explain how to create a backdoor using Seamless SSO and how to exploit it using forged Kerberos tickets.

On October 25th, I’ll be talking at t2.fi infosec conference in Helsinki. In this blog, I’ll tell what to expect in my Abusing Azure Active Directory: Who would you like to be today? presentation.
I was honoured to hear that I was accepted to present my AADInternals toolkit at the most respected information security event in the world: Black Hat USA 2019. This is clearly one of my greatest professional achievements so far! In this blog, I’ll briefly introduce what to expect in my demo at Black Hat Arsenal.
On November 2018 Azure AD MFA was down over 12 hours preventing users from logging in to Office 365. Same happened in October 2019 in US data centers. As MFA is usually mandatory for administrators by company policy, they couldn’t log in either. In this blog, I’ll show how to create a backdoor to Azure AD so you can log in and bypass MFA.
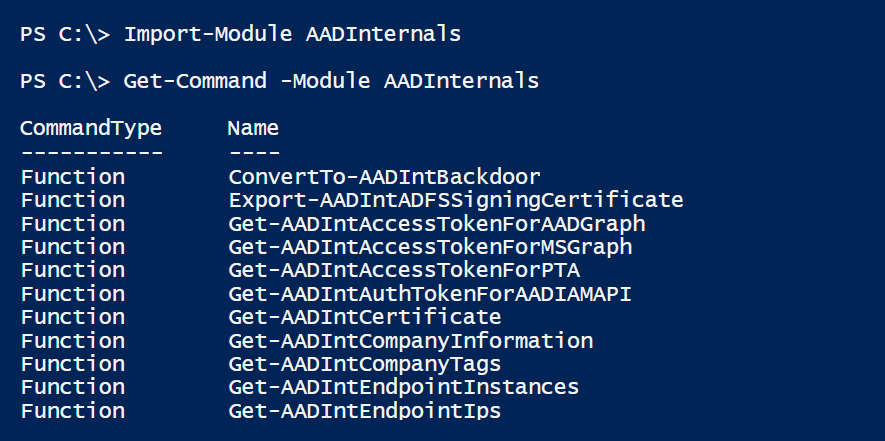
For the last couple months I’ve used most of my free time on studying and hacking Azure AD admin APIs. As a result, I’m finally publishing the first (beta) version of the AADInternals PowerShell module.
By default, any user of Office 365 or Azure AD tenant can read the content of Azure AD using PowerShell and Graph API Explorer. This is a serious security issue because users have undetectable access to other users’ personal data, which violates for instance GDPR. In this blog, I’ll tell how to prevent the access.
Azure AD PowerShell module was earlier installed by a standard .msi package. Now you can install it using one PowerShell command. However, installation requires PowerShell 5 or newer.
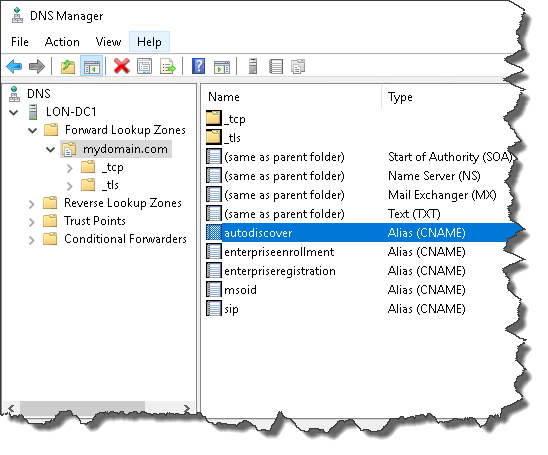
If you are using Microsoft DNS for Office 365 DNS records, you can create the required records easily with PowerShell.
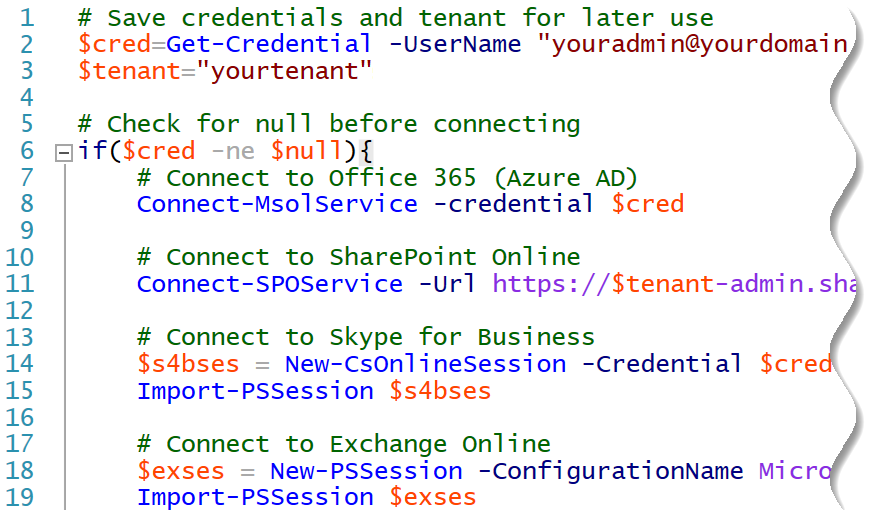
PowerShell profile makes connecting to Office 365 a lot easier!
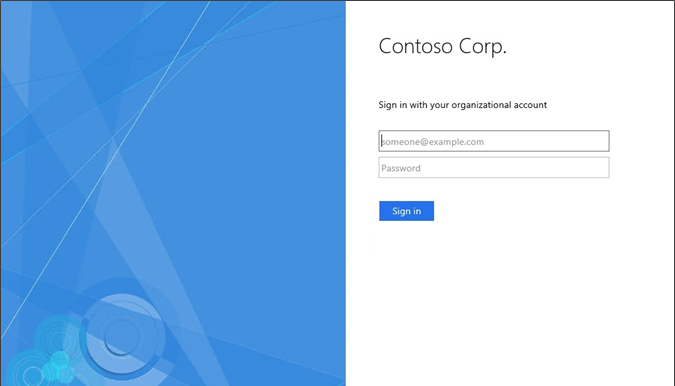
By default, AD FS only supports SSO with Internet Explorer. However, you can easily enable support for Google Chrome, Firefox, and Edge.